AWS Lambda's New Superpower: Automatic Recursion Termination
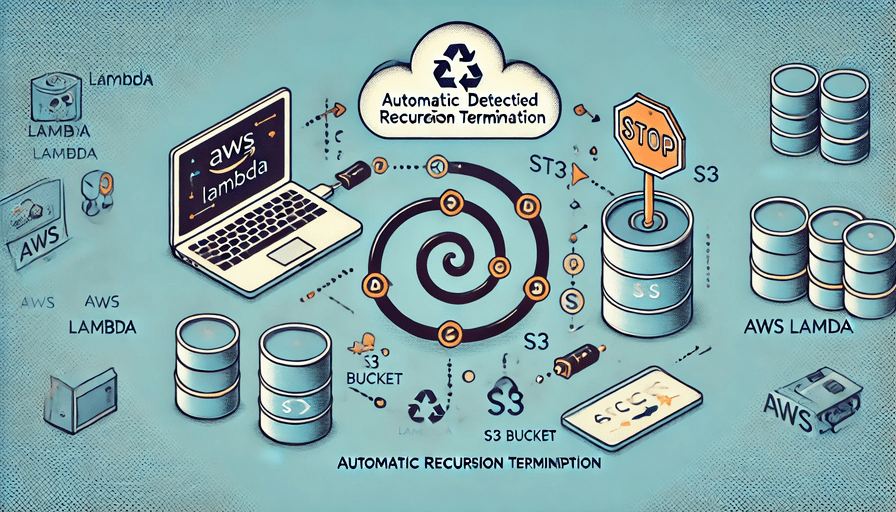
In July 2024, AWS is rolling out a game-changing update to Lambda: automatic detection and termination of recursive loops involving S3. This powerful new feature promises to shield your serverless applications from runaway costs and resource exhaustion. Discover how this update works, why it matters, and how to prepare your applications for this new era of serverless security.
AWS Lambda Recursive Loop Auto Termination: A Game-Changer for Serverless Security
In the ever-evolving landscape of cloud computing, AWS continues to innovate and enhance its services to provide better security and cost management for its users. One such groundbreaking update is the extension of AWS Lambda’s recursive loop detection to include Amazon S3. This change, set to roll out in July 2024, marks a significant step forward in preventing runaway workloads and unexpected costs in serverless architectures.
What’s Changing?
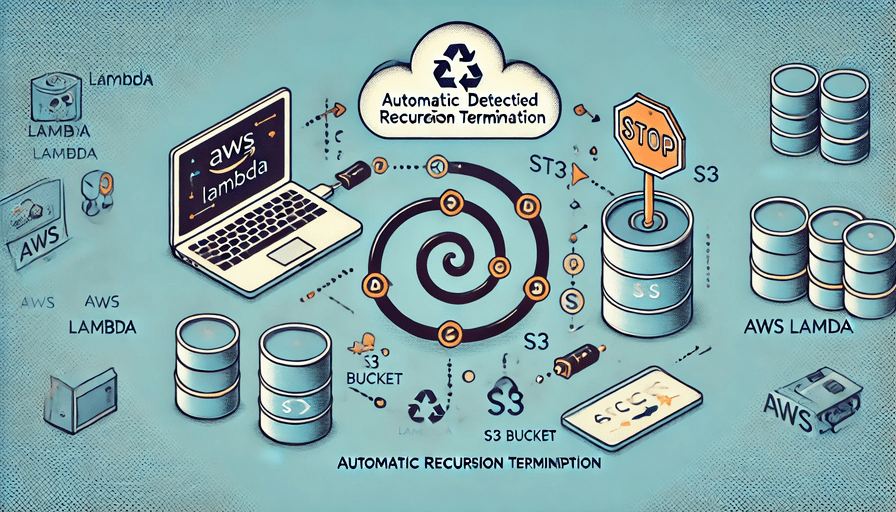
Starting July 8, 2024, AWS Lambda will expand its recursive loop detection capabilities to include loops that pass through Lambda and S3, even when S3 is not the direct event source or trigger for the Lambda function. This means that scenarios like the following will now be automatically detected and terminated:
- A Lambda function stores data in an S3 bucket
- This triggers notifications to SNS
- SNS then triggers the same Lambda function
After approximately 16 recursive invocations, AWS will automatically terminate this loop, preventing potential runaway costs and resource exhaustion.
Why This Matters
Unintentional recursive loops in serverless architectures can lead to several critical issues:
- Unexpected Costs: Rapid, repeated invocations can quickly rack up charges on your AWS bill.
- Resource Exhaustion: Loops can cause Lambda to scale and consume all available concurrency in your account.
- System Instability: Unchecked recursion can lead to unpredictable behavior in your applications.
By automatically detecting and terminating these loops, AWS is providing an additional layer of protection for your serverless applications and your wallet.
How It Works
AWS Lambda uses AWS X-Ray tracing headers to detect recursive loops. Here’s a simplified explanation of the process:
- When supported AWS services send events to Lambda, these events are automatically annotated with metadata.
- When your Lambda function writes an event to another supported service using a compatible AWS SDK version, it updates this metadata.
- The updated metadata includes a count of how many times the event has invoked the function.
- If a function is invoked more than 16 times in the same chain of requests, Lambda automatically stops the next invocation in that chain.
It’s worth noting that this feature doesn’t require you to enable X-Ray active tracing, and there’s no additional charge for using it.
What You Need to Do
For most users, this update will provide an additional safety net with no action required. However, if your application intentionally uses recursive patterns involving S3, you should take the following steps:
- Review your Lambda functions that interact with S3 to identify any intentional recursive patterns.
- If you have functions that rely on intentional recursion with S3, contact AWS Support to opt your account out of recursive loop detection for those specific use cases.
- Ensure you’re using a supported version of the AWS SDK in your Lambda functions. The minimum required versions are:
- Node.js: 2.1147.0 (SDK v2) or 3.105.0 (SDK v3)
- Python: 1.24.46 (boto3) and 1.27.46 (botocore)
- Java 8 and 11: 1.12.200 (SDK v1) or 2.17.135 (SDK v2)
- Java 17: 2.20.81
- Java 21: 2.21.24
- .NET: 3.7.293.0
- Ruby: 3.134.0
- PHP: 3.232.0
- Go: SDK V2 (use latest version)
Best Practices Moving Forward
While this new feature provides an excellent safety net, it’s still crucial to design your serverless applications with recursion in mind. Here are some best practices:
- Implement Guard Rails: Use conditional checks in your Lambda functions to prevent unintended recursion.
- Use Dead-Letter Queues: For functions triggered by SQS, configure a dead-letter queue on the source queue to catch and analyze events that might cause recursion.
- Set Up Monitoring: Use CloudWatch alarms to alert you about unusual patterns in Lambda invocations or concurrency.
- Regular Code Reviews: Consistently review your serverless architecture for potential recursive patterns.
- Test Thoroughly: Implement comprehensive testing, including edge cases that might trigger recursion.
Conclusion
The extension of AWS Lambda’s recursive loop detection to include S3 is a significant enhancement to the security and cost management of serverless applications. By automatically terminating potential runaway processes, AWS is helping developers build more robust and cost-effective solutions.
As serverless architectures continue to grow in popularity, features like this demonstrate AWS’s commitment to improving the developer experience and application security. Stay tuned for the rollout in July 2024, and remember to review your applications for any intentional recursive patterns that might be affected by this change.
Happy serverless coding, and may your functions always terminate as expected!